NSX Advanced Load Balancer - Syslog TLS
NSX Advanced load balancer is simple enough to configure with a remote syslog server entry, but it's a bit more complicated using syslog-tls (SSL).
First, SSH to the NSX ALB Controller to the Avi cli. You can do this 2 ways:
- SSH to the controller using the admin account
- SSH to the controller using the cli account.
SSH as admin.
SSH to admin@controller.ip. Once logged in, type shell, and you will be prompted for credentials again.
1admin@172-30-11-14:~$ shell
2Login: admin
3Password:
4
5[admin:172-30-11-14]: >
SSH using CLI
SSH to cli@controller.ip, then use the admin credentials.
1login as: cli
2Pre-authentication banner message from server:
3|
4| Avi Cloud Controller
5|
6| Avi Networks software, Copyright (C) 2013-2017 by Avi Networks, Inc.
7| All rights reserved.
8|
9| Version: 21.1.1
10| Date: 2021-08-11 17:08:44 UTC
11| Build: 9045
12| Management: 172.30.11.14/24 UP
13| Gateway: 172.30.11.1 DOWN
14|
15|
16|
17End of banner message from server
18
19
20The copyrights to certain works contained in this software are
21owned by other third parties and used and distributed under
22license. Certain components of this software are licensed under
23the GNU General Public License (GPL) version 2.0 or the GNU
24Lesser General Public License (LGPL) Version 2.1. A copy of each
25such license is available at
26http://www.opensource.org/licenses/gpl-2.0.php and
27http://www.opensource.org/licenses/lgpl-2.1.php
28Last login: Wed Mar 23 04:55:59 2022 from 172.31.2.223
29Launching a CLI shell in a container
30Login: admin
31Password:
32
33[admin:172-30-11-14]: >
Help
You can see available commands by double tapping the tab key.
1[admin:172-30-11-14]: >
2attach debug gslb rediscover rollback switchover upload
3clear delete import redistribute rollbackpatch switchto upload_to_avi
4configure do migrate renew rotatekeys system verifylogin
5controller exec passwd resume scalein terminal vinfra
6convert export patch resync scaleout test watch
7core forcedelete reboot retryplacement show upgrade
8[admin:172-30-11-14]: >
Adding certs
Using syslog-tls requires the controller certificate to be listed under Templates / Security / SSL/TLS Certificates, the CA certificates listed under Templates / Security / PKI Profile
Configuring syslog-TLS
1[admin:172-30-11-14]: > configure alertsyslogconfig my-vrli
2[admin:172-30-11-14]: alertsyslogconfig> syslog_servers
3New object being created
4[admin:172-30-11-14]: alertsyslogconfig:syslog_servers> syslog_server 172.30.11.14
5[admin:172-30-11-14]: alertsyslogconfig:syslog_servers> syslog_server_port 6514
6[admin:172-30-11-14]: alertsyslogconfig:syslog_servers> no udp
7[admin:172-30-11-14]: alertsyslogconfig:syslog_servers> tls_enable
8[admin:172-30-11-14]: alertsyslogconfig:syslog_servers> pkiprofile_ref letsencrypt
9[admin:172-30-11-14]: alertsyslogconfig:syslog_servers> ssl_key_and_certificate_ref LetsEncrypt-20220224
10[admin:172-30-11-14]: alertsyslogconfig:syslog_servers> save
11[admin:172-30-11-14]: alertsyslogconfig> where
12Tenant: admin
13Cloud: Default-Cloud
14+-------------------------------+----------------------+
15| Field | Value |
16+-------------------------------+----------------------+
17| name | my-vrli |
18| syslog_servers[1] | |
19| syslog_server | 172.30.11.14 |
20| syslog_server_port | 6514 |
21| udp | False |
22| tls_enable | True |
23| ssl_key_and_certificate_ref | LetsEncrypt-20220224 |
24| pkiprofile_ref | letsencrypt |
25+-------------------------------+----------------------+
26[admin:172-30-11-14]: alertsyslogconfig> save
27+-------------------------------+--------------------------------------------------------+
28| Field | Value |
29+-------------------------------+--------------------------------------------------------+
30| uuid | alertsyslogconfig-e78d261d-eae6-46d0-8fa4-f416ecd2da32 |
31| name | my-vrli |
32| syslog_servers[1] | |
33| syslog_server | 172.30.11.14 |
34| syslog_server_port | 6514 |
35| udp | False |
36| format | SYSLOG_LEGACY |
37| tls_enable | True |
38| ssl_key_and_certificate_ref | LetsEncrypt-20220224 |
39| pkiprofile_ref | letsencrypt |
40| anon_auth | False |
41| tenant_ref | admin |
42+-------------------------------+--------------------------------------------------------+
Navigating and making changes
To see the configuration, use the show alertsyslogconfig command.
To set a field to True, just type the name.
To remove, or set a field to False, type no udp
To edit an existing item, specifiy the field. Using tab completion should show the option.
For sub-items, specify the keyword index, with the index number:
ie: syslog_servers index 1
To remove a sub-item:
no syslog_servers index 2
Troubleshooting
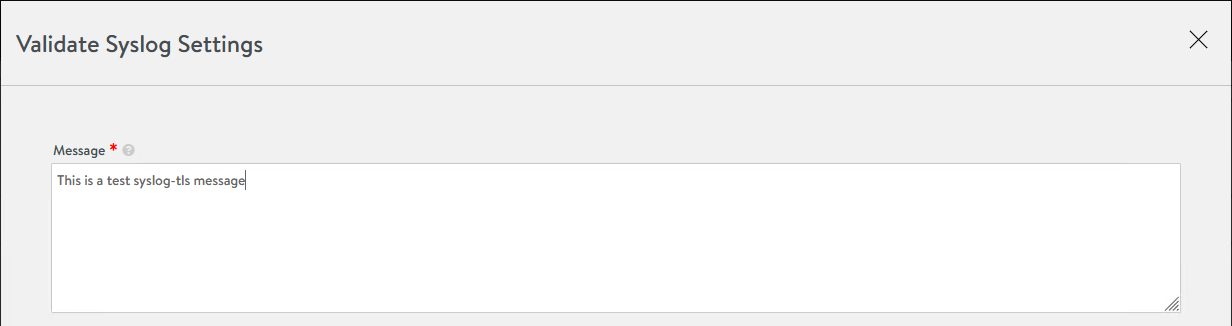
Go to Operation / Notifications / Syslog, and click the Question mark [?]. In the Validate Syslog settings, you can send a test message to the remote syslog server.
To confirm packets are being sent to the remote syslog server, you can use tcpdump:
1admin@172-30-11-14:/var/log$ sudo tcpdump host 172.30.11.13
Where 172.30.11.13 is my vRealize Log Insight server.
pkiprofile_ref: If you have spaces in the name, using tab autocomplete will fix it with My\ Profile\ With\ Spaces, but it doesn't save it. Rename the PKI profile within the UI, and try again.